Living in the Information Age, as we do today, brings with it a lot of convenience and benefits, but it also comes with a lot of risks. On the one hand, humanity has access to virtually all of the information and knowledge known in existence with a few clicks of a button; on the other hand, this great power in the hands of a nefarious few can cause great destruction and misery if abused. In this article, I’ll walk you through the various steps you can take to protect your personal information online.
Some may dismiss this as “tin-foil hat” thinking, but as we’ve seen with many three-letter organisations around the world, government spying has progressed from being regarded as a crazy conspiracy theory to being nearly openly acknowledged. As a result, those who value privacy and want to remain as anonymous as possible will find Linux to be a valuable tool when used properly. Indeed, for those who want to remain as anonymous as possible online, Linux is the only option, as Windows and Mac OS X are notorious for collecting as much information on you as possible.
You can see this for yourself by performing a Google search for “Windows 10 spying” or “Mac OS X privacy.” Before we begin, it’s important to note that the only computer that is completely secure and private is one that is disconnected from the Internet or turned off. As a result, it is impossible for a device connected to the Internet to be completely secure. There is always a way around security, and if there isn’t, tools are constantly being developed to discover new ones. So the guiding principle here is not to expect to change a few settings on your computer and think you’ve now enabled your Impenetrable Fortress, but rather to put up as many roadblocks as possible to make it as difficult as possible for any would-be attacker or spy to gain access to your system or private information.
There are a few Linux tools that can be used to maintain as much anonymity as possible (again, in today’s day and age, this is becoming increasingly difficult, but if privacy is important to you, you already know the importance of fighting the good fight and refusing to go gently into that good night):
Tails OS
The first tool we’ll look at is Tails OS, though “tool” may be the wrong adjective because Tails is an entire Linux Distro, not just a tool. Tails is intended to be an anonymous, self-destructing operating system that vanishes and leaves no trace of its existence once you’ve finished using it. Obviously, this makes it less than ideal for use as a daily driver, but if you need to access something online and prefer to keep it private or want to browse anonymously, Tails is a great place to start. Rather than being permanently installed on your hard drive, Tails operates entirely as a Live system, erasing itself upon shutdown.
You can get the most recent Tails ISO from the aforementioned link and either burn it to a DVD or copy it to a bootable flash drive (the latter is much easier, less time consuming, and less wasteful). Linux includes several tools for burning DVDs, the most notable of which are Brasero and DeVeDe. If you prefer to create a bootable flash drive, Unetbootin may be ideal (or you can use the ‘dd’ command in the terminal if you’re familiar with it).
Once Tails has been copied to a bootable medium, simply boot your computer from it as if you were installing a new operating system or running a Live system.
The Tails website appears to only allow you to download Tails using Firefox or Tor Browser. When I attempted to download the ISO using Google Chrome, it informed me that my browser is not supported. It also forces you to install their Firefox browser add-on, which automatically verifies your ISO download upon completion using checksum verification. This is a great security measure to put in place because it prevents you from receiving a corrupted copy of Tails that may contain security holes, as happened with Linux Mint.

Once you’ve booted into Tails, it will walk you through some simple initial setup steps. Consult the documentation if you are unsure. Tails’ key feature is that all Internet connections are automatically routed through the Tor network, increasing your anonymity even further. If you’re not familiar with the Tor network, we’ll go over it later when we talk about Tor Browser. Another important feature built into Tails is MAC address spoofing, which we’ll go over in greater detail when we talk about the macchanger tool.

To summarise, Tails is the way to go if you need a temporary, Live OS that erases itself upon shutdown (think Mission Impossible’s self-destructing messages, but much less dramatic). Make sure to visit Tails’ website for more in-depth information.
Tor Browser

Tor Browser, a product of the Tor Project, an organisation dedicated to online privacy and security, is the next tool we’ll look at. As previously stated, this tool is already included with Tails OS, but you can install it on any operating system you prefer, as versions for Windows, Mac, and Linux are available. As far as I know, it is unlikely to be found in any official Linux repositories, so you’ll need to download it from their website links above.
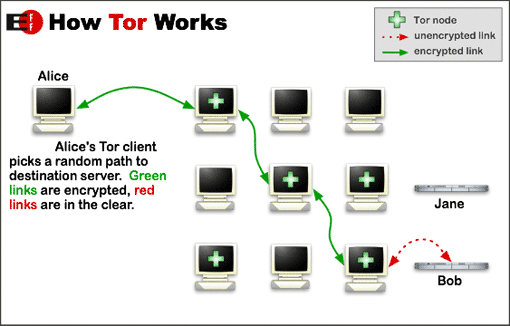
A typical Internet connection directs traffic from the host requesting information to the server providing the requested information, with a few extra hops from server to server in between to ensure that the traffic reaches its intended destination. This, on the other hand, can be easily tracked, even if you’ve deleted your browsing history.
Tor Browser, on the other hand, routes your traffic to many, many different intermediary servers within the Tor Network, known as nodes, which serve to obfuscate the original source of the traffic before exiting the Tor Network via an exit node and finally arriving at the intended destination. As you might expect, this slows down your browsing speed slightly, but if privacy is a concern, one can learn to live with sacrificing a little speed for anonymous web browsing. It is recommended that you use Tor Browser only when a specific task or tasks necessitate extra caution, rather than using it as your daily driver.
Tor Browser is a fork of Firefox, so you can install your favourite add-ons like Adblock Plus, uBlock Origin, DownThemAll, and so on, but keep in mind that any additional add-ons you install may weaken Tor’s security, putting you at risk and defeating the purpose of using it in the first place. Take care in deciding what you want to install. In fact, Tor strongly discourages the installation of any browser plug-ins.
Tor Browser can also bypass web filters if you live in a country where the Internet is censored, such as China. Some hidden websites, dubbed “onions,” have obscure URLs and can only be accessed through Tor Browser. The now-defunct Silk Road, for example, was one of these onions because it could only be accessed via Tor Browser (the author does not condone drug use of any kind, I am merely presenting an example that many people are likely to have heard of). If you use a regular browser to access these links, you will be unable to find them.
Furthermore, some websites, such as Twitter, can detect Tor Network traffic, making it nearly impossible to maintain an anonymous Twitter account, as Twitter will require you to provide a phone number if you attempt to create and use a Twitter account via Tor.
It’s also worth noting that Tor Browser isn’t a magic “hide me” button. It is still possible for your browsing habits to be tracked. Be wise, be cautious, and keep in mind that everything you do on a computer leaves a trail somewhere, whether you like it or not.
It is also worth noting that the FBI discovered an undisclosed exploit in Tor Browser that allowed them to track and arrest people. So, until the Tor Project team discovers and fixes this exploit, Tor remains weakened and vulnerable, despite being far superior to a standard browser. As a result, using Tor without also running Tails OS may be a bad idea. Use discretion and prudence.
On Android, there’s also Orbot, a mobile Tor solution that uses the OrFox browser. Both are available for download on Google Play and F-Droid.
VPNs are also worth investigating if you want to increase the security of your web traffic.
macchanger And MAC Spoofing
When it comes to Internet traffic, there are two types of addresses: IP Addresses and MAC Addresses. You’re probably already familiar with your IP Address, but you might not be so familiar with your MAC Address. IP addresses are typically assigned automatically by a network’s router or DHCP server (your home router has a DHCP Server built in). This is your network address, which can change at any time.
You could also set a static IP address that does not change rather than having one assigned to you automatically (this is generally ideal for printers and other shared peripherals on a network). You’ll also have an internal IP address that only exists on your local network (likely 192.168.1.x or 192.168.0.x) as well as an external IP address that all of your incoming and outgoing traffic uses (go to IPChicken if you want to see your external address).
There are, however, MAC Addresses in addition to IP Addresses. MAC addresses, unlike IP addresses, are physically burned into networking equipment and cannot be changed. Because of this, MAC addresses are also referred to as hardware addresses. Internet traffic uses both your IP Address and MAC Address to determine where data should be routed. As a result, in addition to obfuscating your IP Address with Tor Browser, it’s a good idea to obfuscate your MAC Address with MAC Spoofing.
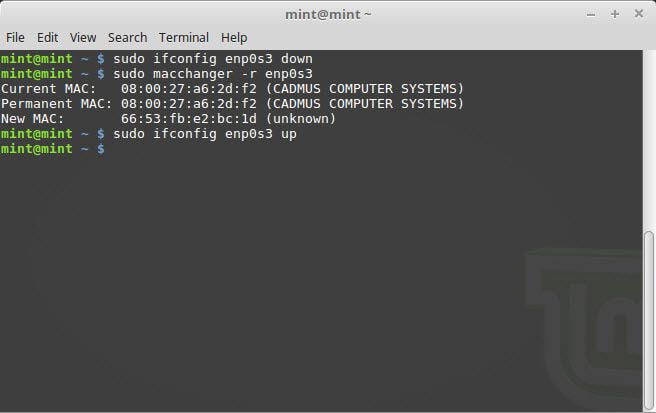
Again, unlike your IP Address, you cannot change your MAC Address; however, you can spoof your MAC Address so that it appears to be something else. As previously stated, this is something that is already built into Tails OS, but it is also possible to do on other distros. Macchanger, a simple terminal command that allows you to spoof your MAC address as you see fit, is my preferred tool. If it isn’t in your official repositories (sudo apt-get install macchanger), you can get it from GitHub or the GNU website.
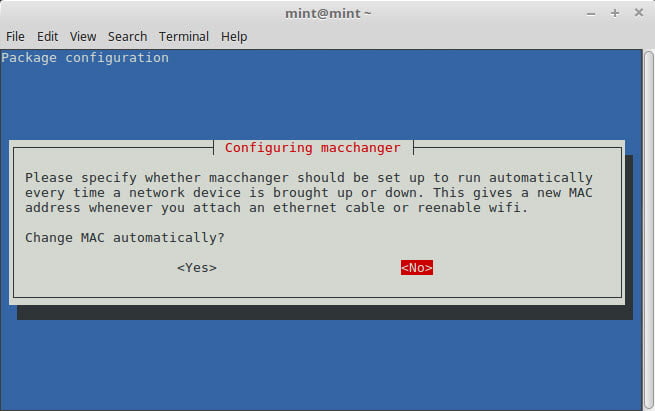
The -r (random) flag is the simplest way to use macchanger to generate a random MAC address, but in my experience with Ubuntu 14.04 LTS, I could never get this to work. The command would be carried out, but the MAC address would never change. However, this was a long time ago, and macchanger appears to have been updated since then. It appears to work just fine in Linux Mint as of this writing, and the developer(s) have even added an automatic function for your MAC to change every time the device is restarted, making it easier than ever before.
When your device restarts, it will appear to have a different MAC address, indicating that the address has been spoofed. This, in conjunction with Tor Browser and/or Tails OS, will obfuscate your online presence to the greatest extent possible.
Full Disk Encryption
Full Disk Encryption is a complicated process that I still don’t fully comprehend. To summarise, if you want to encrypt your data, Full Disk Encryption is the way to go, as it prevents anyone from physically accessing any data on your hard drive without the encryption passphrase.
There are numerous methods for manually configuring Full Disk Encryption, but they are all far beyond my comprehension. As a result, the simplest way to enable Full Disk Encryption is during the installation of your Linux distribution.
If you use Ubuntu or Linux Mint, you’ll notice that on the Installation Type screen, beneath Install Ubuntu, there are two checkboxes that say “Encrypt the new Ubuntu installation for security” and “Use LVM (Logical Volume Management) with the new Ubuntu/Mint installation.” In general, I will check both of these boxes and let Ubuntu/Mint handle the rest. However, if you prefer to use your own custom partitioning scheme, you will be unable to do so here because this option will cause Ubuntu/Mint to handle partitioning for you. It is still possible to go to Something Else and create your own encrypted partitions, but this becomes a bit more complicated and would require a separate article.

This procedure may be available in other distros, but my personal experience has been limited to Ubuntu and Mint.
If you simply want to encrypt specific folders on your Linux system, another useful utility is encfs, which should be available in the official repositories. You can use Encfs to create an encrypted folder that cannot be opened or viewed without the encryption passphrase. Note that this does not completely remove the encrypted folder from your system, as a clever person could still identify it (you can probably figure it out too if you know where to look), but they would be unable to access its contents without the passphrase. VeraCrypt, which has replaced the popular but now-defunct TrueCrypt, is another popular encryption tool.
And, of course, there’s the obligatory XKCD.
Conclusion
As you can see, Linux provides a wide range of privacy and security solutions. What has been discussed here are only the fundamentals; the advanced user is likely to discover other, more complicated yet robust methods of security. However, for the average user, these tools can provide a useful balance of usability and security. Please leave a comment if you have any questions, comments, or concerns, or if you know of any other useful tools that were not mentioned above.