There may be times where logging in to a computer remotely is necessary. You may require access to a file, need to assist a friend with a problem, or even transfer files between computers. Whatever it is Secure Shell (SSH) lets you connect to another computer running Linux (or indeed another Unix system like BSD or Solaris) over an encrypted connection. For a remote host to receive SSH connections, it must have the daemon running (sshd) and you must have it accept incoming packets to port 22 if a firewall is used.
How SSH Works
The idea behind SSH is to allow a user to remotely interact with a computer via the terminal over an encrypted connection. This means that data transmitted (like the username and password used to login) is secure, thus preventing an attacker from easily collecting sensitive data using a packet sniffer, which would be the case if you were using Remote Shell (RSH) over the Internet because your login details would be sent to the server as plain text (no encryption).
Setup SSH
If your computer isn’t able to receive SSH connections, you will need to install the SSH protocol if it isn’t already installed. Systems like Ubuntu should configure the SSH daemon (sshd) to run on startup. If there is a firewall present, you may also need to configure the settings to allow incoming connections to port 22 or whichever port you have chosen SSH to accept incoming connections.
$ sudo apt install ssh
A Simple Demonstration
As with many things with Linux, the process of logging into a remote shell is simple. Let’s open a terminal and login into a machine under the username “unix_allsort”:
$ ssh unix_allsort@remotehost
If this is the first time you have logged in to a particular host using your computer under the current user, it will ask you if you wish to accept that host to the list of known connections. If it isn’t and you get that message, it could be a different host altogether, which could possibly indicate someone is masquerading as that computer!
Once you have authenticated yourself, you should then be able to navigate your way around the system like you would if you were at the computer in person.

You could even use SSH on that computer to access another remote computer:
unix_allsort@remotehost:~$ ssh user@anotherremotepc
Running Programs On Remote Hosts OR SSH Execute Remote Command
There is an option to run an application on a remote host once logged in using SSH. An example would be to launch an editor to edit a particular file on the said host.
$ ssh -t unix_allsort@remotehost vim ~/Documents/list.txt
You would be able to use vim like you would if you were using that computer in person. The ‘-t’ option is required whenever you wish to launch programs like vim from a remote host. This parameter is used to force pseudo-terminal allocation. The man page states that screen-based programs, like vim, should be launched with this option for that reason. If this is missing, some terminal apps may not function correctly.

GUI Applications
SSH also provides a way to launch an X11 GUI program, like Firefox, as opposed to a text-only program.
$ ssh -X unix_allsort@remotehost
Firefox The ‘-X’ parameter simply tells the remote host to allow the connecting computer to launch many X applications when commanded to do so, either via the shell or otherwise. Many programs can be run this way, web browsers, editors, even some Windows programs via Wine. I have found that terminal emulators on X refuse to run. Also, refer to the man page for more information about X11 forwarding.
Note: You may encounter this error when logging using SSH with X11 forwarding enabled: /usr/bin/xauth: timeout in locking authority file /home/your_home/.Xauthority If this ever occurs, the problem is that a lock file for ‘xauth’ already exists. The solution is to remove the lock file. There may be more than one so run this command to remove them (forcibly if necessary):
$ rm -rf ~/.Xauthority-*
Log out of the SSH session and log back in again. You should then be able to run X apps again.
Configuring SSH With No Password
It is possible to remotely login to a computer without having to enter your credentials. This requires that computers be set up to allow your computer to login in such a way, achievable through the use of key-pairs generated using ‘ssh-keygen’.
First, the key needs to be generated. Here, it is acceptable to stick with the defaults. Since the point of this exercise is to skip entering any password or passphrase in the terminal each time a session is initiated, we wish to have no passphrase for this key.

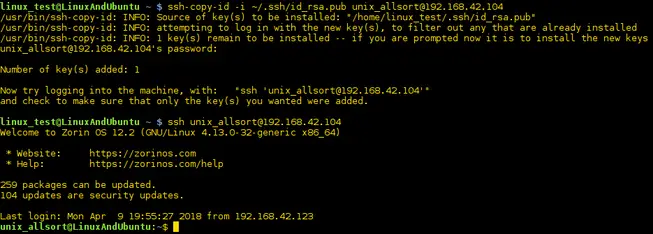
After everything has been created, the ky found in the identity file needs to be installed onto the remote computer:
$ ssh-copy-id -i ~/.ssh/id_rsa.pub user@remotehost
If these steps were performed correctly, you should be able to login via SSH into the PC without being prompted for a password.
Tools that rely on SSH
Secure Copy
SCP (Secure Copy) enables users to copy files to or from a remote host over a secure connection. The syntax is very similar to the ‘cp’ command where you specify the files or folders and their destination. Here is an example:
$ scp ~/Documents/shopping.odt unix_allsort@remotehostname:~/Documents
We’ve just copied a file over the Internet through a secure connection to a remote computer. The same can be done for folders as well:
$ scp -r unix_allsort@remotehostname:~/Documents/Reports ~/Documents
This copies a folder (hence the ‘-r’ for recursive) and its contents from a remote PC to your computer.
SSH File Transfer Protocol (SFTP)
SFTP allows secure access and transmission of files using the file transfer protocol via SSH.
Conclusion
With SSH you are able to easily login to another computer from almost anywhere under normal circumstances. X11 forwarding can be enabled to run GUI apps off the remote machine, and programs can be launched instead of launching a shell. The man page for SSH provides much useful information, so do have a look at it.
