I have written an article covering privacy-centric Linux distros. Today I used Septor Linux, a distro designed to surf the Internet anonymously. I would have extended the list to the 6 best privacy-centric Linux distro if I had used it earlier.
As I said above that there are already Linux distros that focus on users’ privacy. What is different or unique in Septor, how does it make users anonymous, and what tools it uses? We’ll discuss it all in this article?
Based on Debian, KDE Plasma, And Tor
Septor Linux is based on Debian and uses Tor technologies to make users anonymous online. Septor 2019.4 has Linux kernel 4.19 and a customized version of KDE Plasma 5.14.3.
If you do not know what Tor is, you can read this guide to know Tor in detail. But in short, the Tor network transfers users’ requests through different other Tor clients used by people in other parts of the World, which makes users completely anonymous. Due to this nature of transferring requests through many clients, it is also called the onion network.
Septor Routes all traffic through Tor
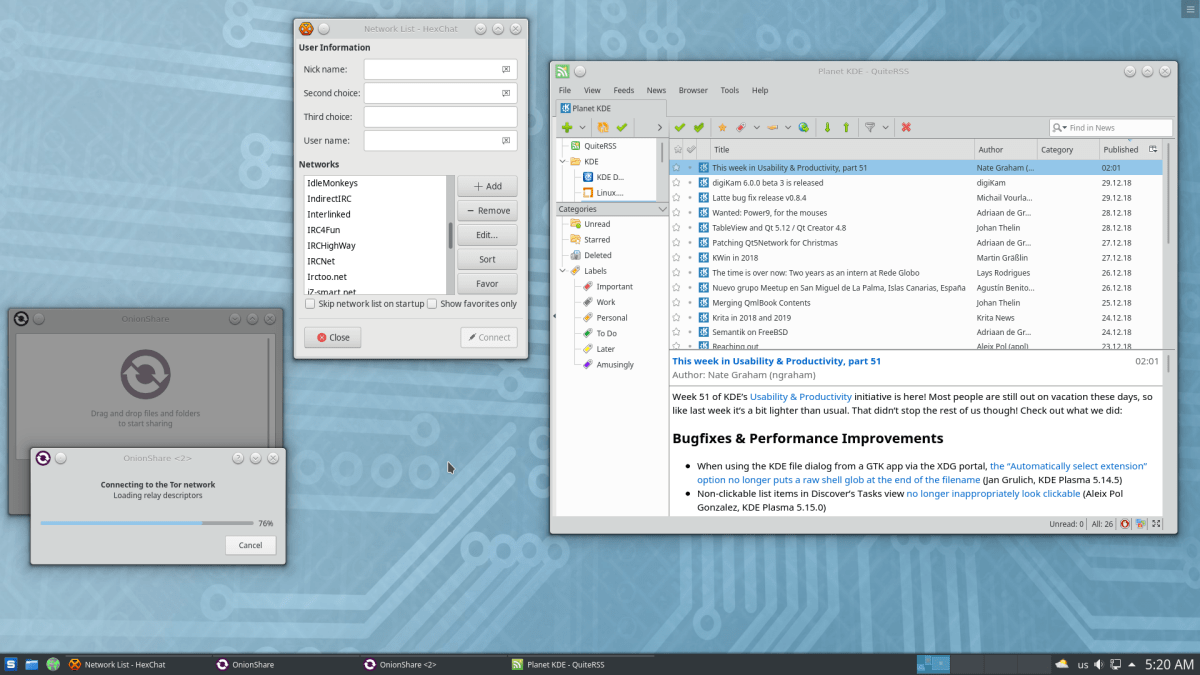
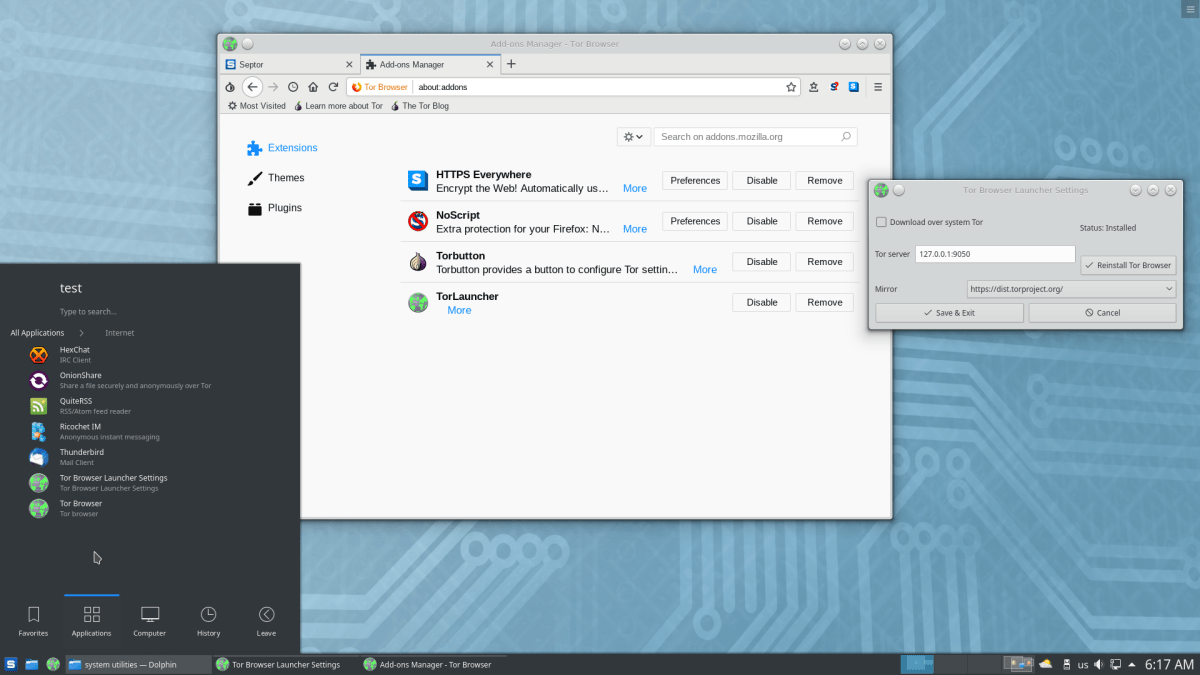
Septor Linux either includes tools already built to use tor, or the team configures other tools to use Tor to gain complete anonymity. For example, the Tor web browser and OnionShare are already preconfigured to use Tor for anonymity.
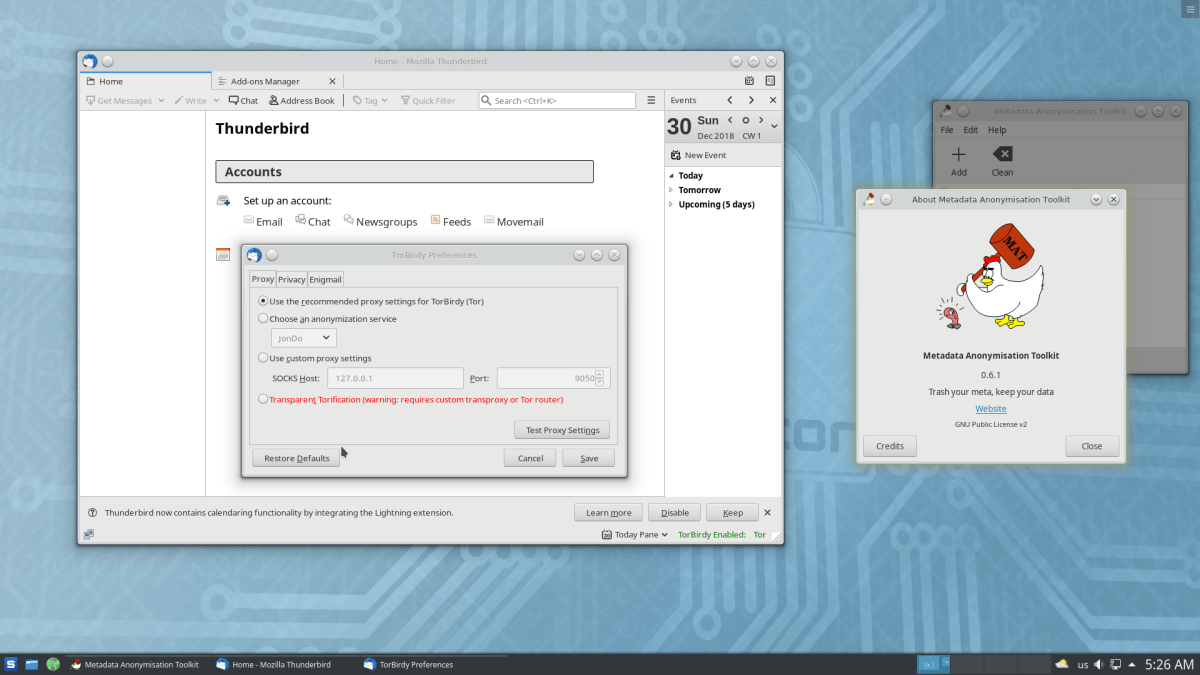
And secondly, the tools that the Septor team has configured to use Tor to gain anonymity, for example, Thunderbird has TorBirdy preinstalled to route traffic through Tor. So this way, Septor routes all the internet traffic through Tor.
Besides these apps, Septor has a wide collection of daily-use apps — from music player, graphics tools like GIMP, LibreOffice, KWallet to VeraCrypt for files encryption and so on…
Is it better than Tails?
So finally, the question arises if it is better than other privacy-centric Linux distros, especially Tails. Well, Septor has a nice concept of using Tor to route traffic, but it lacks behind compared to Tails and other privacy-centric distros.
First of all, Septor configures all the applications to use Tor which is great, but what about the data that stays when you shut down your computer. Tails Linux runs scripts on shutdown event that wipes out private data from memory.
Septor does not use any approach to wipe out private data from memory on system shutdown.
Secondly, the idea behind running a live system is getting a system up and ready as soon as it boots up. Septor does not come with any web browser but Tor launcher that you run to install Tor web browser.
Edit – Unfortunately, I had an older of Septor, which I used to test on VM. Septor team had included Tor browser 8.5.4 back in February 2019.
And third is the community. Septor official website provides very little information about the distro, and it has no forum for discussion or features highlights. On the other hand, Tails and other privacy-centric distros have properly put out information on their website, and their community support is also excellent.
If you run into any problem with Septor, there is no specific forum to post your problem. You can, of course, post your questions in Debian forums since it’s Debian-based, but that’s not a Septor community, and it might find difficult to understand Septor specific errors.
Septor needs many improvements, from providing a web browser that makes the distro up and running on live boot to providing an informative website and community support.